SecurOS® FaceX as a Credential
A Facial Recognition and Authentication Solution for Access Control Deployments
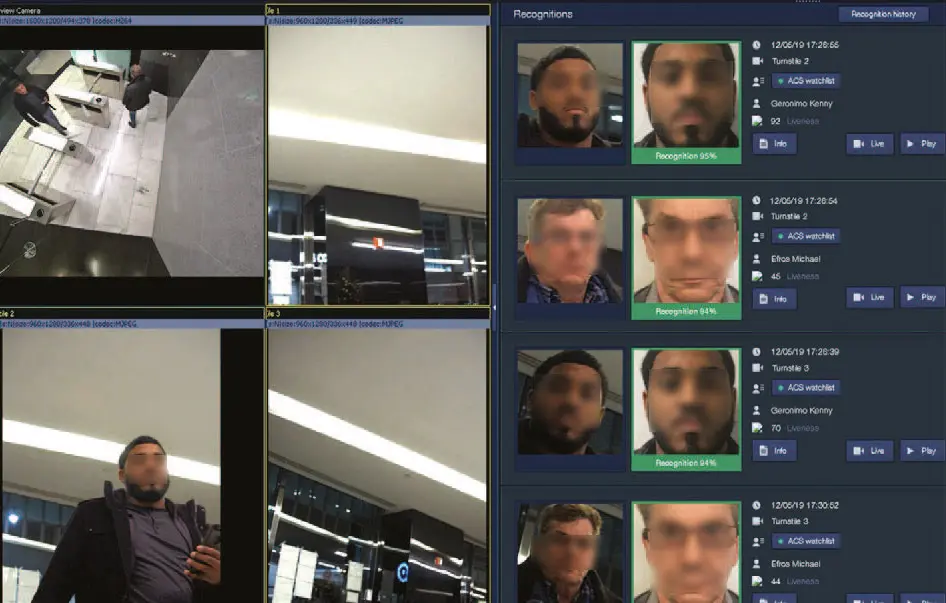
The SecurOS® FaceX as a Credential (FaaC) system from ISS enables organizations to use the faces of employees, contractors and guests to create a frictionless/hands-free access control solution all while leveraging existing hardware components to keep deployment costs low. Faces can also be combined with other credentials, such as proximity cards and biometric readers, to provide multi-factor authentication for high security applications.
Additionally, our anti-spoofing technology checks for face liveness, and ensures that printed photos or images from mobile devices will be flagged. The unique FaaC solution can also incorporate standard, off-the-shelf cameras and other security appliances to minimize investment, maintain building aesthetics, and eliminate excessive labor related to user enrollment and credential management.

Technology Overview
Unlimited Database Size
Convolutional Neural Network-Based Algorithms
Data Security
Key Features
Multifactor Authentication
Special mode to manage access control systems (ACS) for both single-factor and multifactor authentication.
Anti-spoofing
Check for face liveness, and ensure that printed photos or images from mobile devices (phone, tablet) will be flagged as spoofing alarms.
Seamless Integration with ACS Systems
Existing integrations with all major access control systems.
Single Enrollment Interface
Synchronize ACS Person database with SecurOS® FaceX Person database to provide a single enrollment interface.
High Performance in Low Light
System performs well in low-light and does not require additional lighting fixtures to be installed at doors/turnstiles.
Speed of Entry
Whole process of face detection/recognition and opening the door/turnstile is done in less than 500 ms.
A Frictionless
Access Control Solution
White Paper
ISS Face Recognition as a Credential in Access Control Deployments
Facial recognition can be used for various applications such as access control, recognizing known criminals or people of interest, and providing increased security for high risk facilities related to both inside and outside threats. Today, facial recognition is considered the most natural of all biometric measurements, and for good reason.Download the SecurOS® FaceX as a Credential datasheet
Key Applications

Commercial Buildings

Government
